We secure your AI,
SixWays to Sunday.
Three ways we shield you. Three ways we strike back.
Tool Calls Today
1,842
Auto-Approved
1,791
Human Approvals
33
Denied
18
Governance Decisions
09:36:28
MCP Proxy
Claude Code: tools/call "bash" with rm -rf. Destructive action requires approval
Pending
09:36:21
Risk Profile
User jsmith escalated T1 to T2. Score: 0 to 25 after sandbox violation
Escalated
09:36:14
MCP Proxy
Cursor: tools/call "git push --force" on main branch. Denied by org policy
Denied
09:35:58
MCP Proxy
Copilot: tools/call "npm install lodash" approved. Package in allowlist
Approved
09:35:42
Policy Push
Updated Claude Code managed-settings.json on 12 endpoints. SHA-256 verified
Synced
09:35:18
MCP Proxy
Gemini CLI: tools/call "kubectl apply" requires human approval. Approved by admin
Approved
T1 Kinetic
T2 Semantic
T3 Cognitive
Recent Detections
09:36:14
T2 Semantic
Prompt injection via vector similarity (0.91). PII redacted
from response stream.
Redacted
09:36:18
T1 Kinetic
Egress: AWS credential pattern detected in Cursor response
via Aho-Corasick.
Redacted
09:35:41
T3 Cognitive
Shadow audit flagged social engineering intent. User risk
score escalated.
Escalated
09:35:02
T1 Kinetic
Slopsquatting: unknown package "reaqt-dom" not in
allowlist.
Blocked
09:34:47
T1 Kinetic
Egress: Private key pattern (-----BEGIN RSA) detected in
Copilot response.
Redacted
09:34:12
T2 Semantic
Presidio NER: 3 email addresses and 1 SSN detected in agent
output. Confidence 0.94.
Redacted
Active Containers
34
eBPF Sidecars
34
Syscalls/sec
8,421
Violations Today
7
Active Sandboxes
sandbox-0a4f Claude Code
Wolfi devcontainer / seccomp: 214 allowed / uptime 47m
sandbox-1b3e Cursor
Wolfi node / seccomp: 214 allowed / uptime 23m
sandbox-2c5d Aider
Wolfi python / seccomp: 214 allowed / uptime 8m
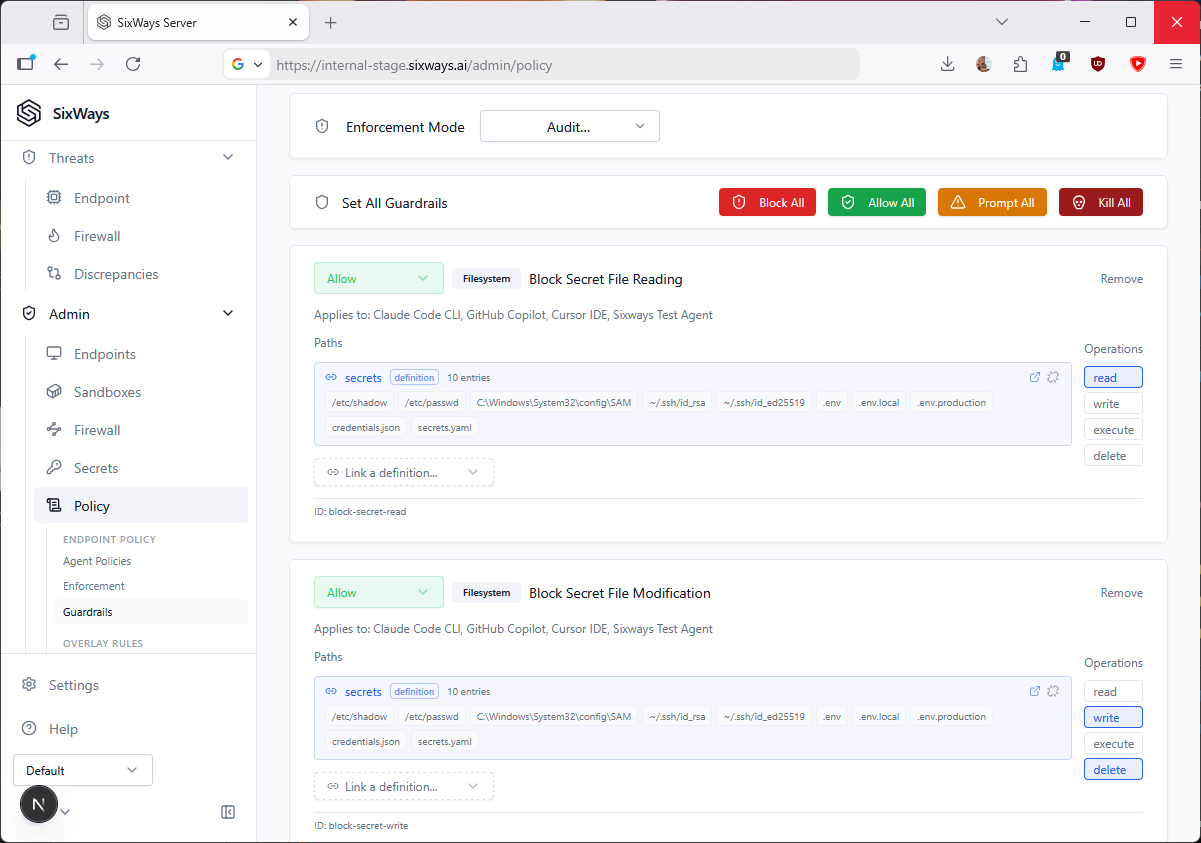
Active Policies
14
Guardrail Rules
86
Agent Configs
5
Last Push
3m ago
Policy Hierarchy
Organization: Default Policy
Block secret file reads / sandbox code execution / redact PII
Group: Engineering
Allow npm/pip registries / block pastebin.com / sandbox all
CLI agents
User Override: jsmith
Elevated access to staging APIs / temporary exception expires
in 4h
Endpoint: dev-laptop-3d6e
Container sandbox required / block host-level execution /
Gemini CLI restricted
Process Lineage
claude_code
PID 2841
→
python3
PID 3412
→
bash
PID 4519
→
git
PID 5231
curl
PID 6100
System Activity Timeline
10:00:00
- 10:00:50
10:00:32
:00:10:20:30:40:50
Processes
Network
TCP
api.anthropic.com
TCP github.com
Filesystem
Read src/main.rs
Write
config.json
Read
~/.ssh/id_rsa
Input
Type
'import subprocess...'
Type
'chmod +x run.sh'
Event Details
bash
(PID 4519) | 10:00:28
Process ID
4519
Parent
python3 (3412)
Command
/bin/bash -c "chmod +x scripts/run.sh"
FS Write
Network
TCP to github.com
eBPF Verdict
BLOCKED
Reason
Unauthorized file read: ~/.ssh/id_rsa
Agents Terminated
3
Sessions Severed
5
Credentials Revoked
4
Avg Response Time
1.2s
Recent Sever Events
09:36:12
Process Kill
Claude Code (sandbox-0a4f) terminated. Unauthorized read on
~/.ssh/id_rsa
Severed
09:35:41
Session Revoke
Cursor (dev-laptop-2c5d) session invalidated. Behavioral
anomaly score exceeded threshold
Severed
09:34:18
Container Freeze
sandbox-2c5d frozen and queued for forensic snapshot.
Outbound exfiltration attempt detected
Frozen
09:33:02
Credential Revoke
API token for jsmith revoked across 3 endpoints. Telemetry
submitted to server
Revoked
08:47:55
Process Kill
Aider (sandbox-3f8a) terminated. Attempted write to
/etc/hosts
Severed
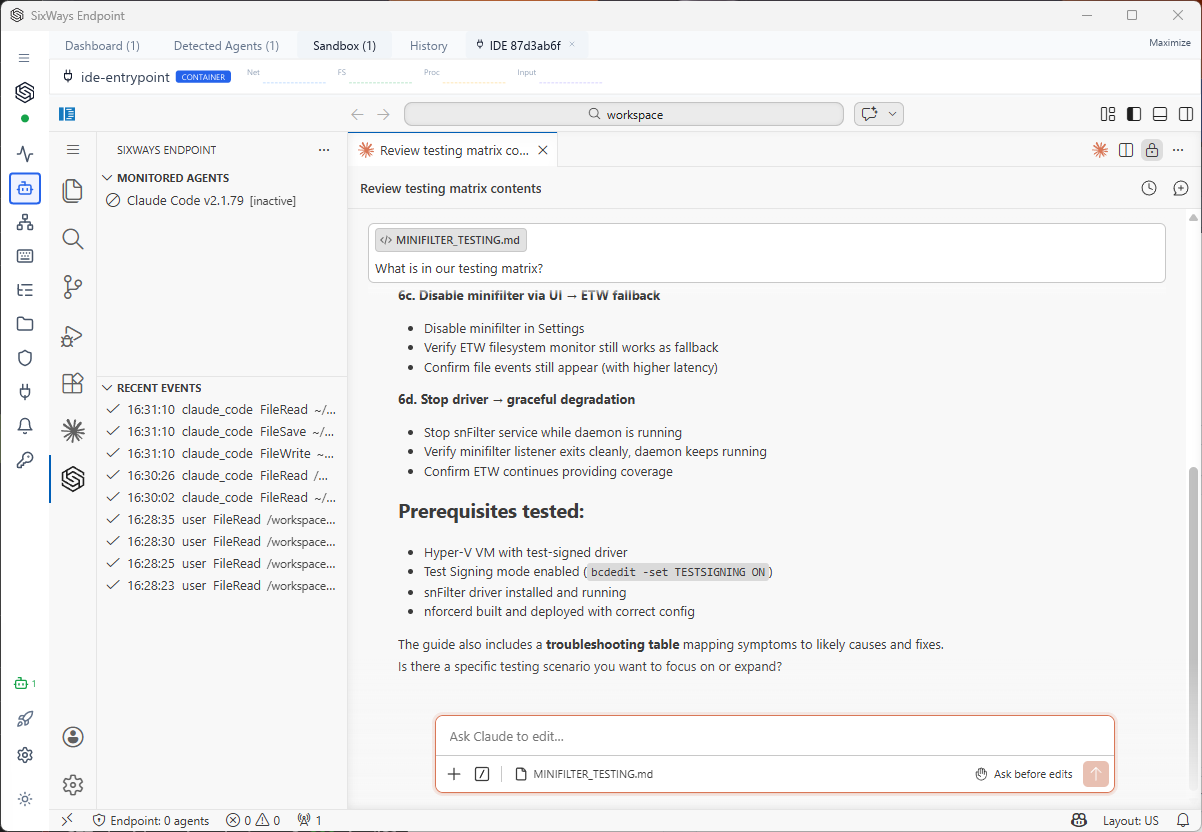
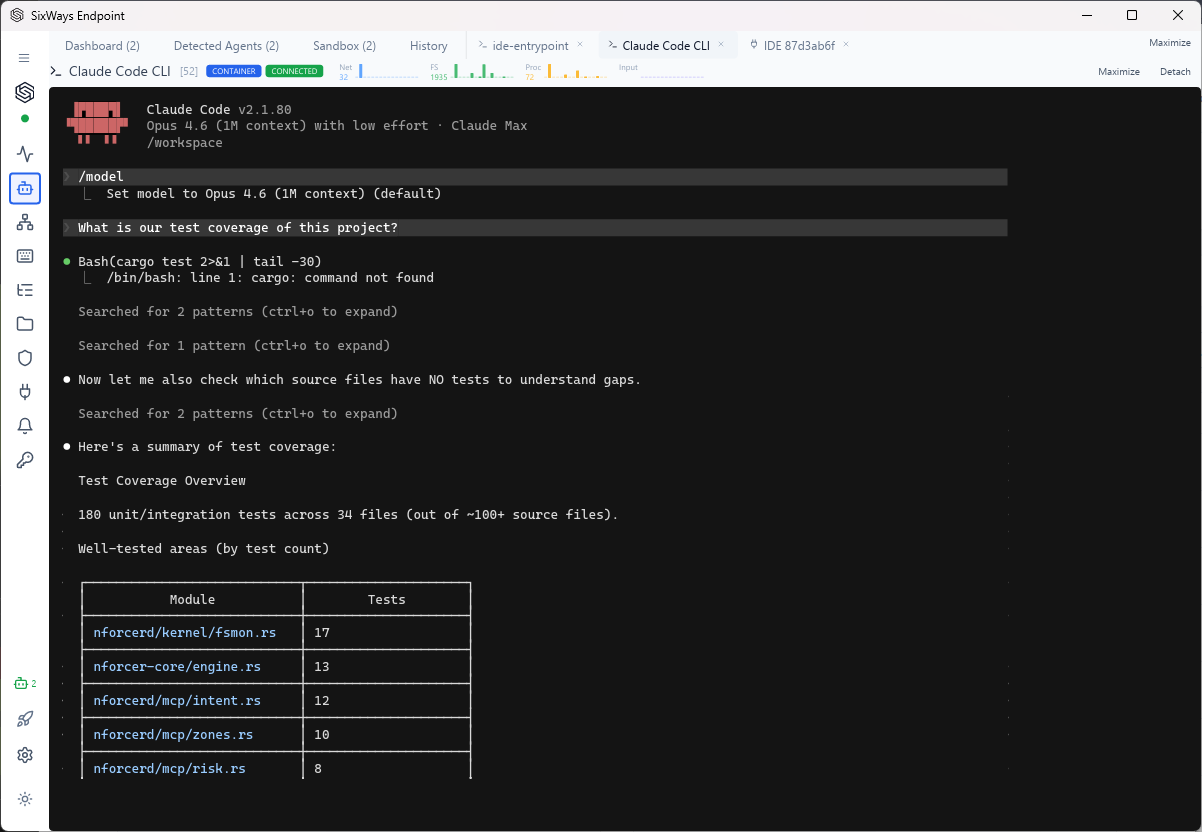
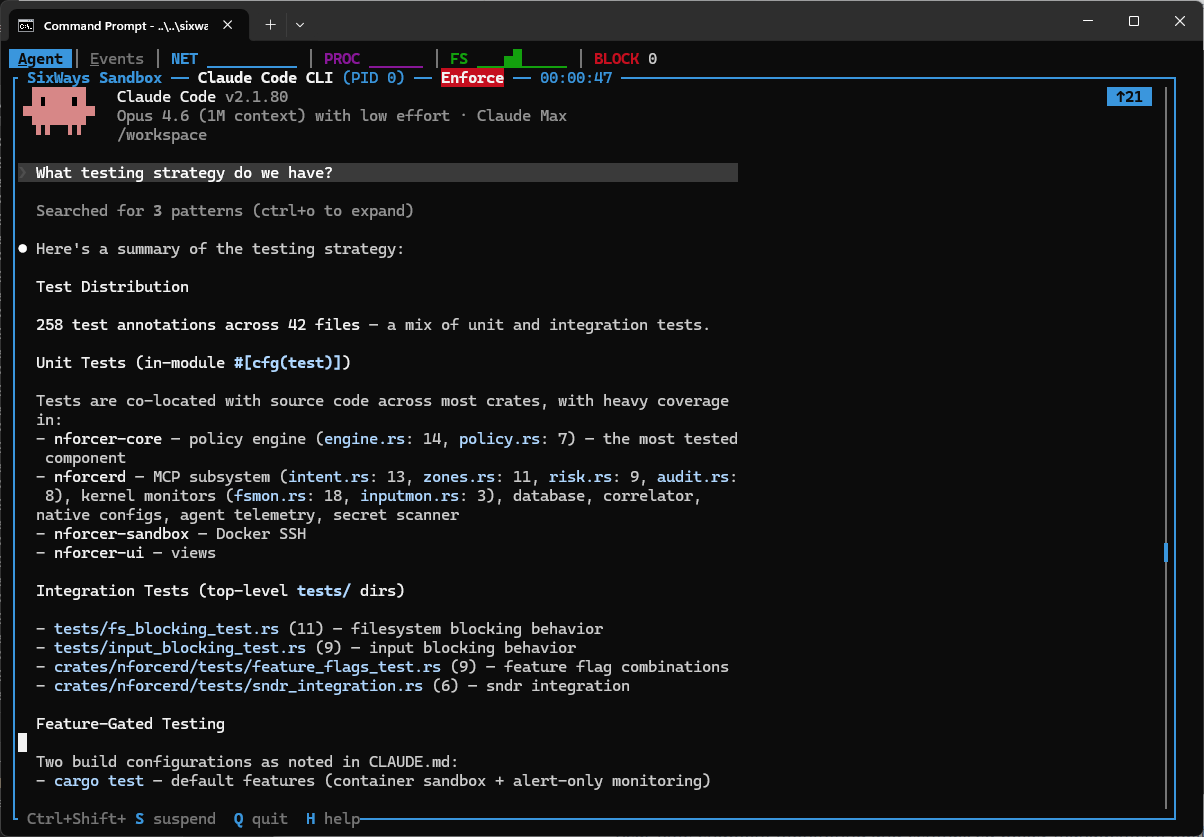
Monitor. See everything your AI agents do. Replay any session like a DVR with
synchronized process lineage, network activity, filesystem access, and chat transcript. Scrub to any
point, bookmark key moments, and fast-forward at up to 8x speed. Built for incident response, compliance
audits, and debugging.